Project Screenshots
Cross-platform infrastructure automation across Ubuntu 24.04 LTS and Windows Server 2025 — hardening, user management, secrets encryption, and CI/CD via GitHub Actions. One command configures everything.
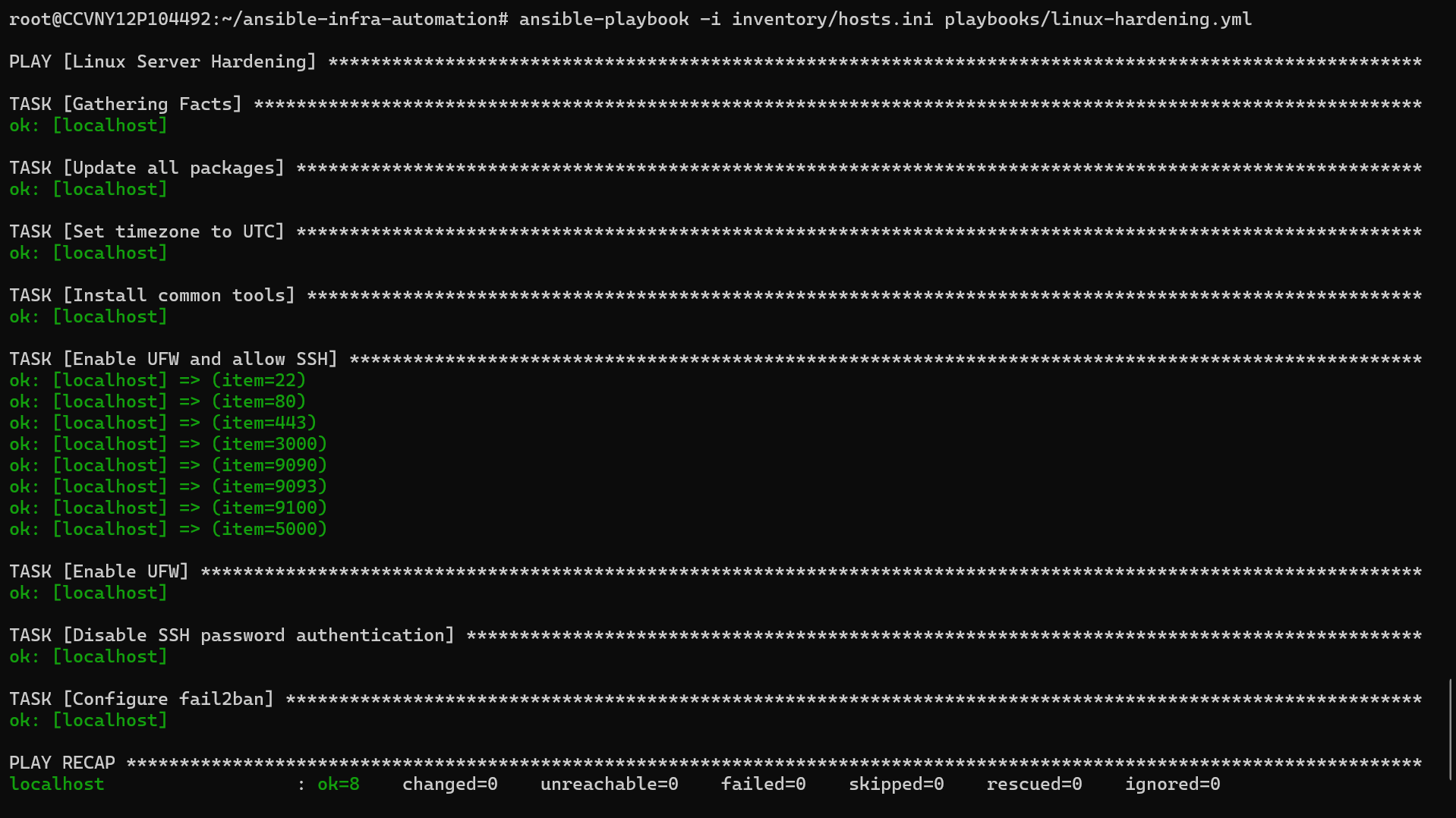
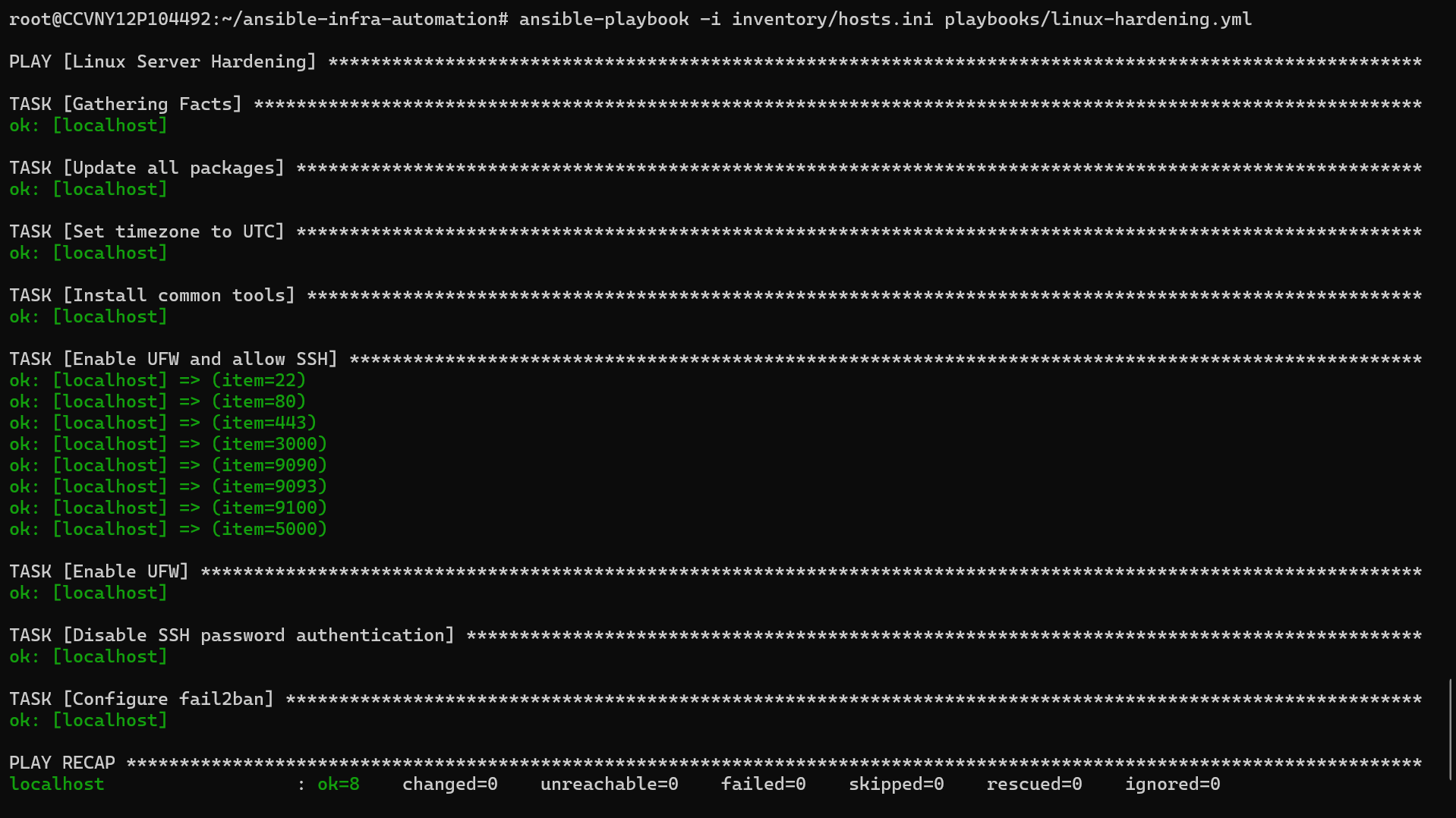
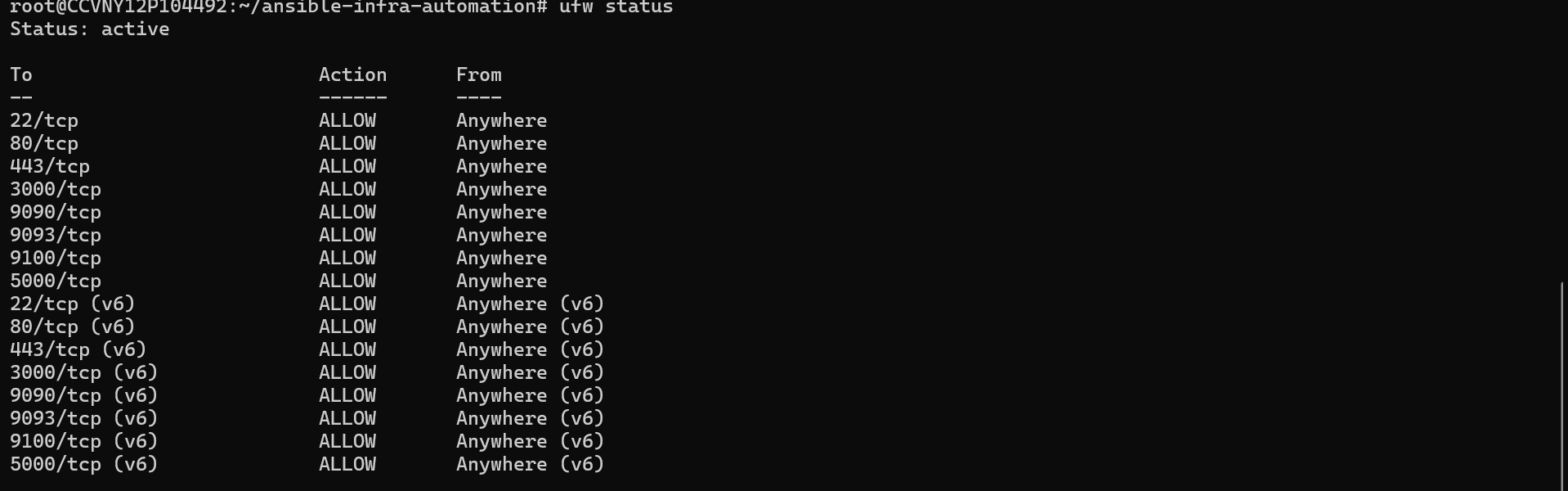
UFW firewall rules, fail2ban intrusion prevention, SSH key-only auth, system package upgrades, and common tooling installation on Ubuntu 24.04 LTS.
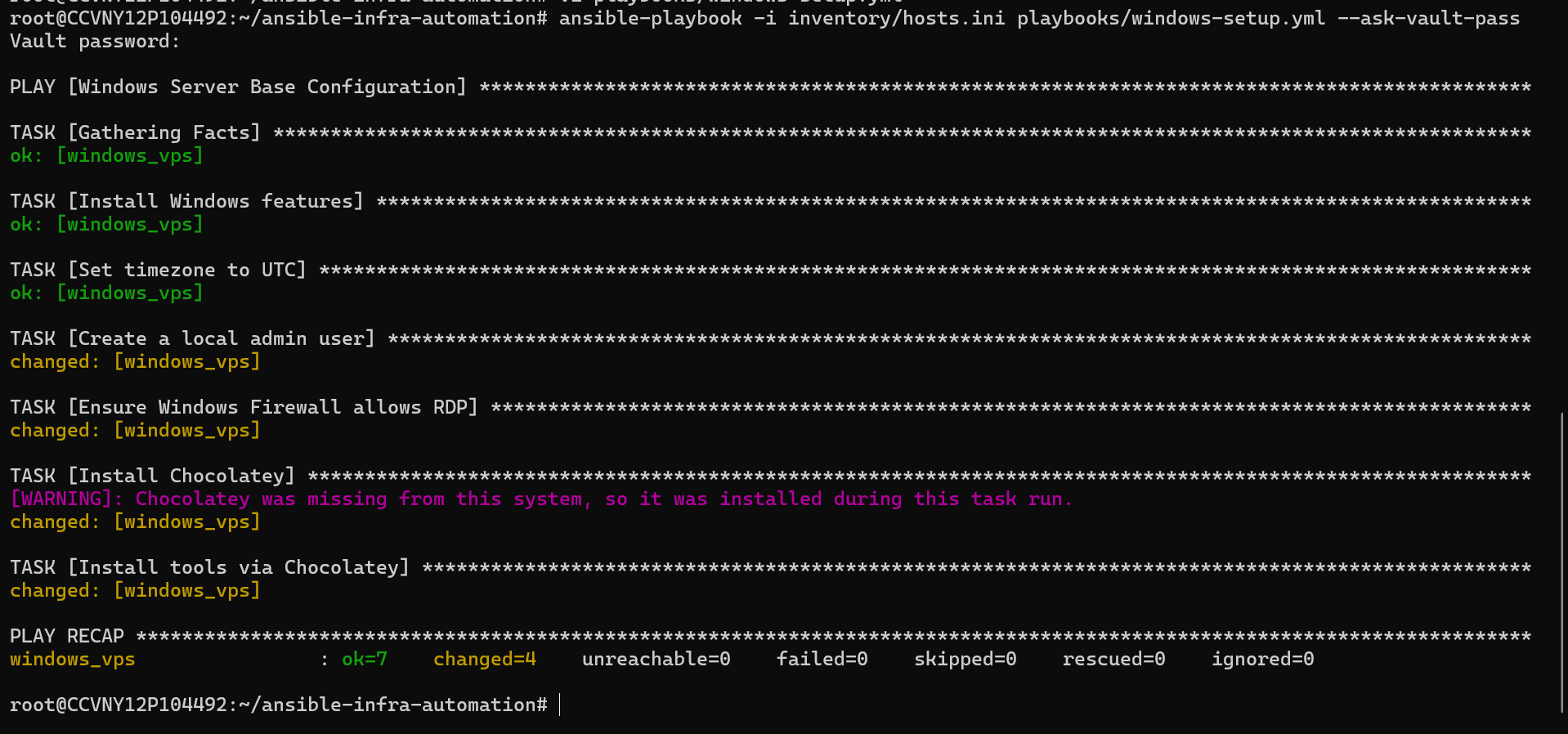
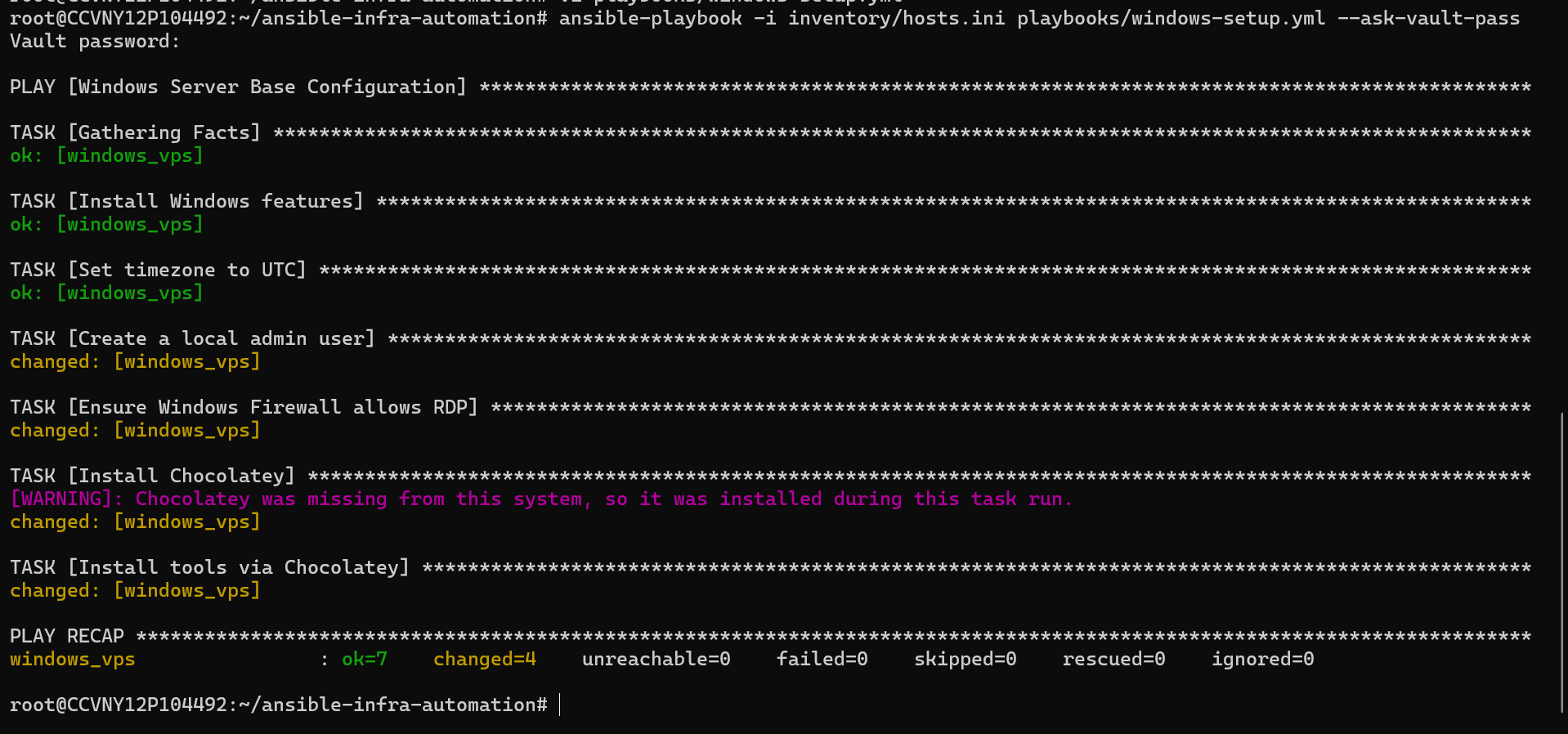
WinRM-based remote automation of Windows Server 2025 — user creation, firewall rules, IIS feature install, timezone config, and Chocolatey package management.
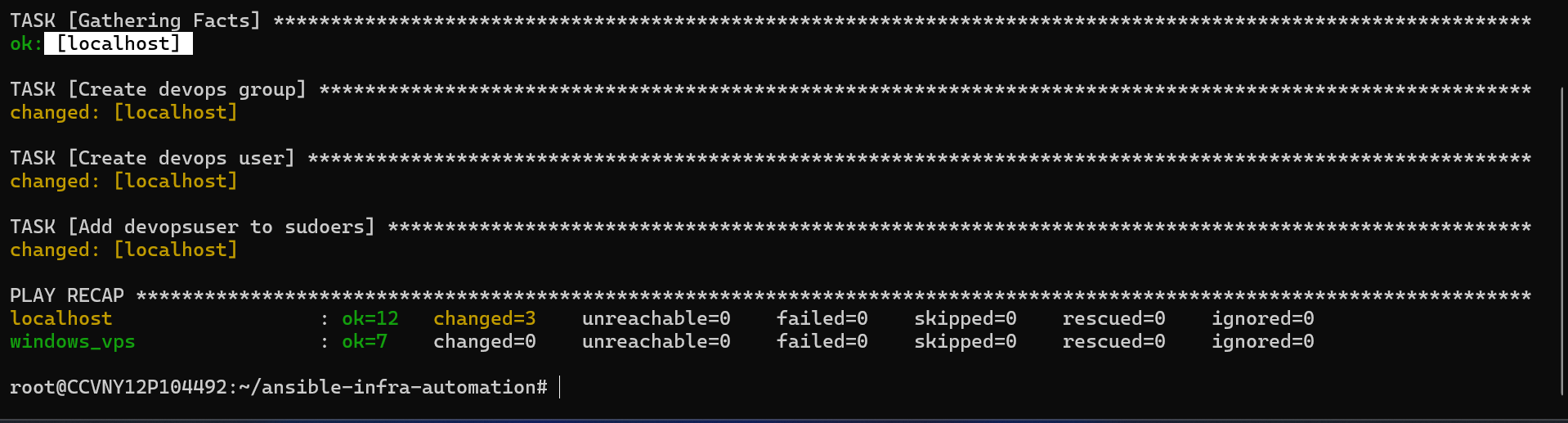
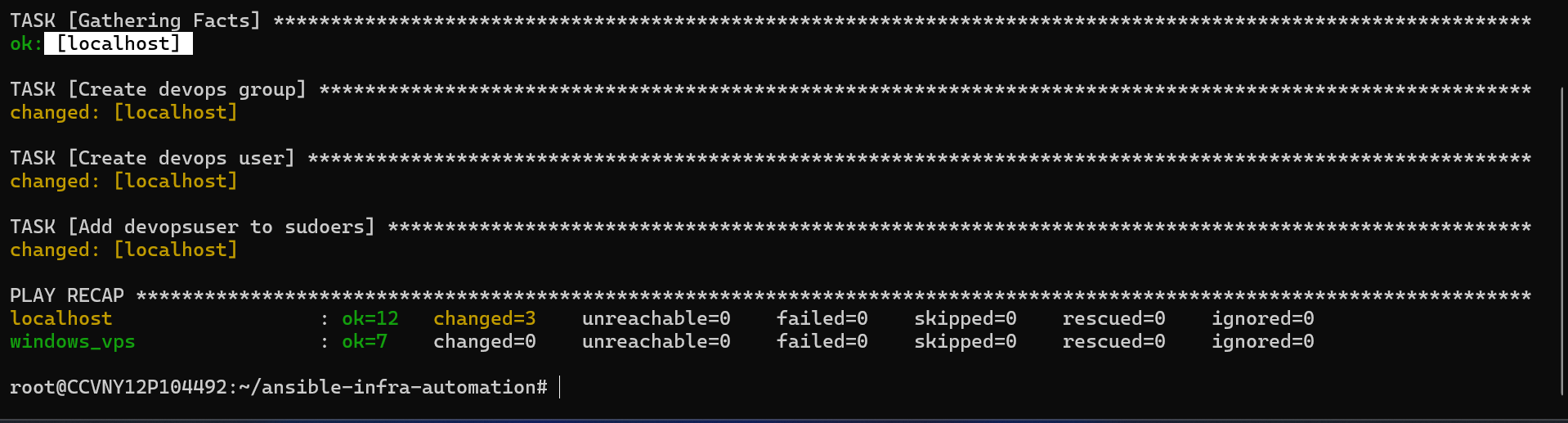
Automated devops user and group creation with sudoers configuration on Linux — mirrors real-world onboarding automation used by infra teams.
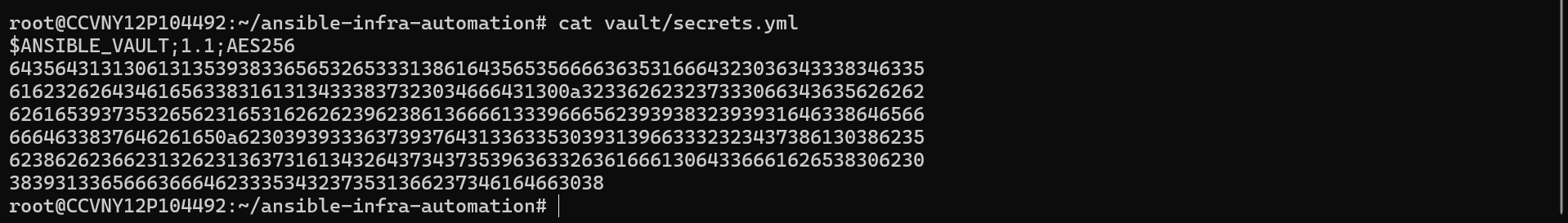
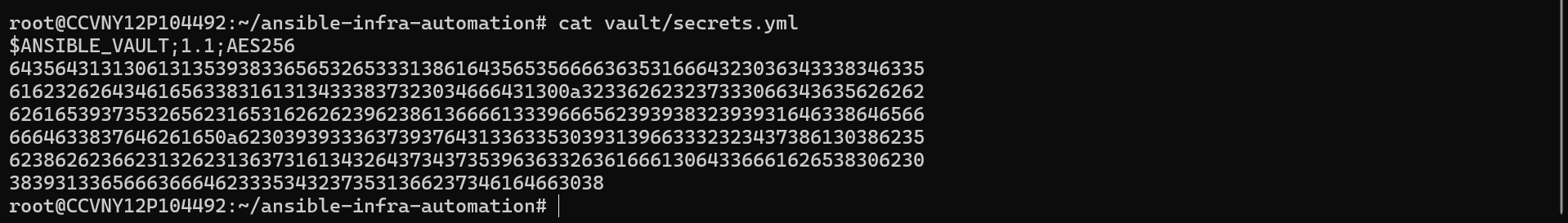
Sensitive credentials encrypted with AES-256 Ansible Vault. Secrets never stored in plaintext — vault file committed safely to version control.
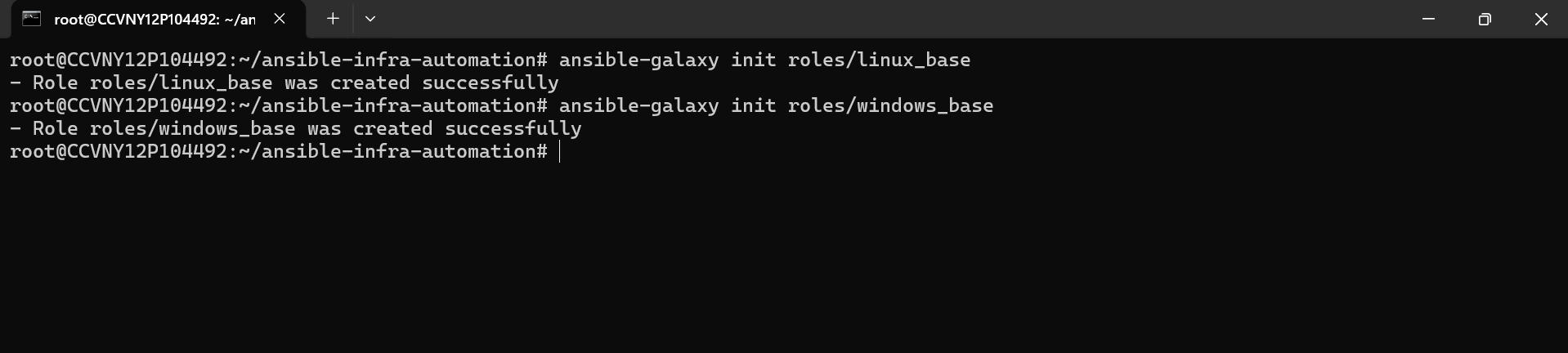
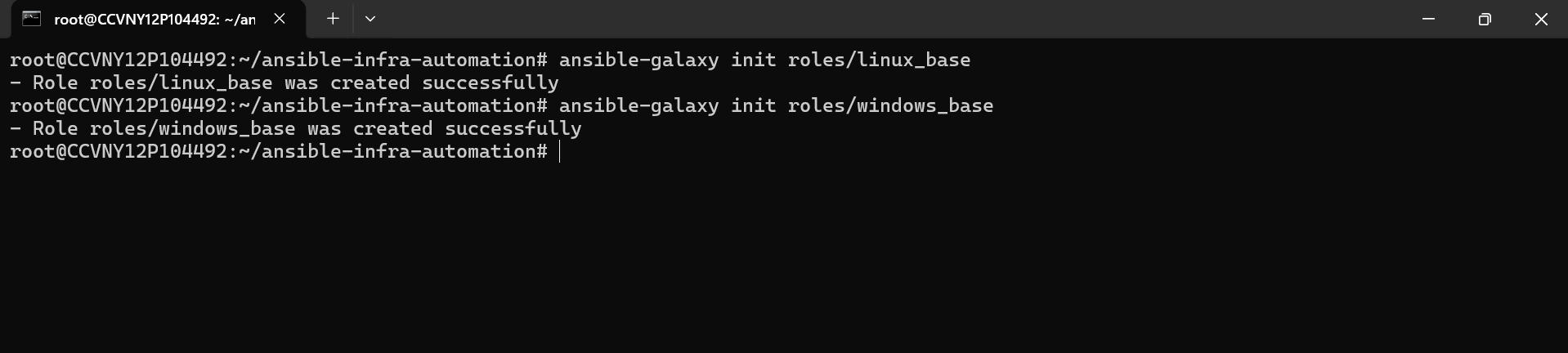
Enterprise-grade role structure using ansible-galaxy — linux_base and windows_base roles for reusable, modular configuration management.
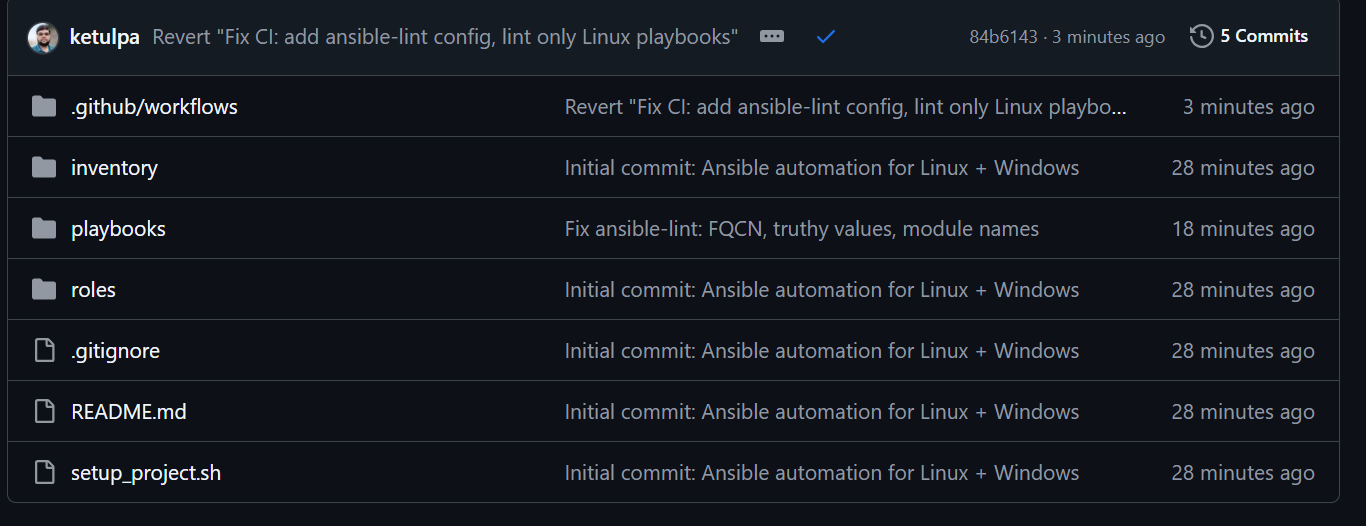
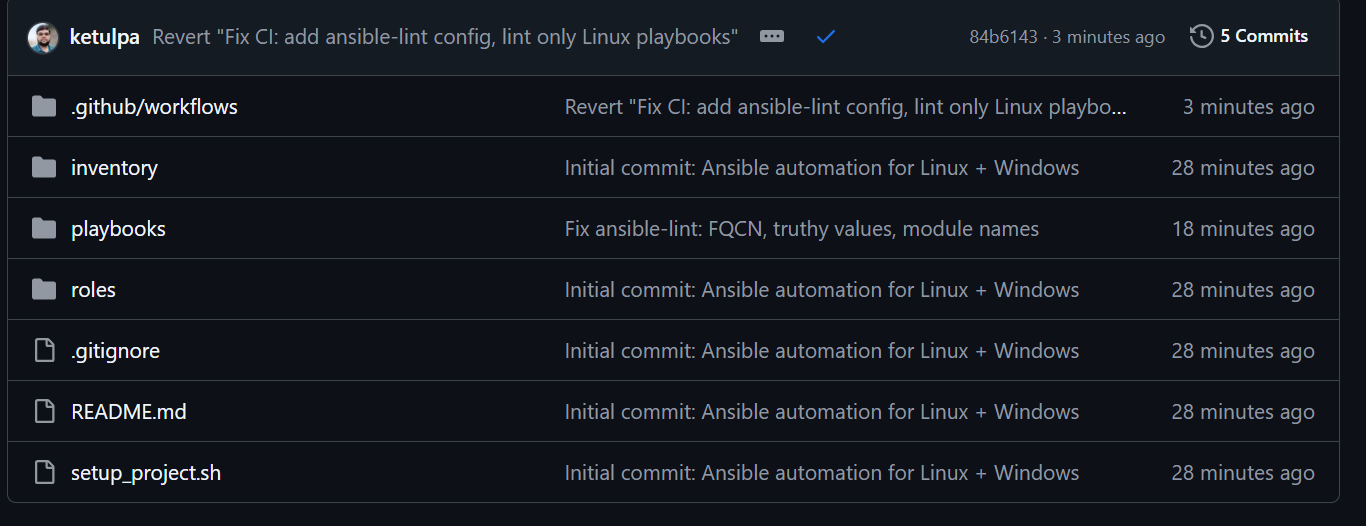
ansible-lint runs automatically on every push — enforcing FQCN standards, YAML formatting, and playbook syntax before any code reaches production.
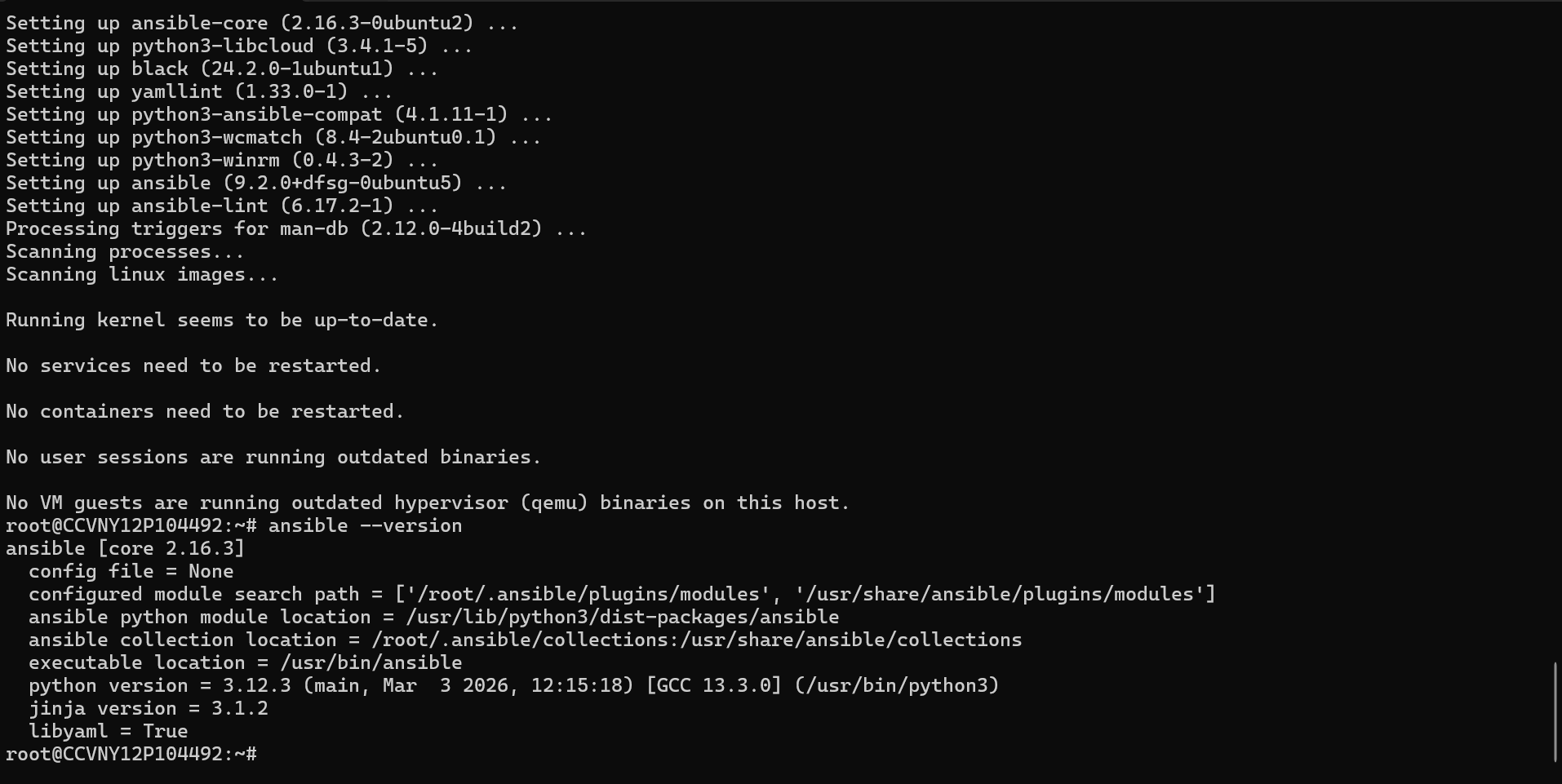
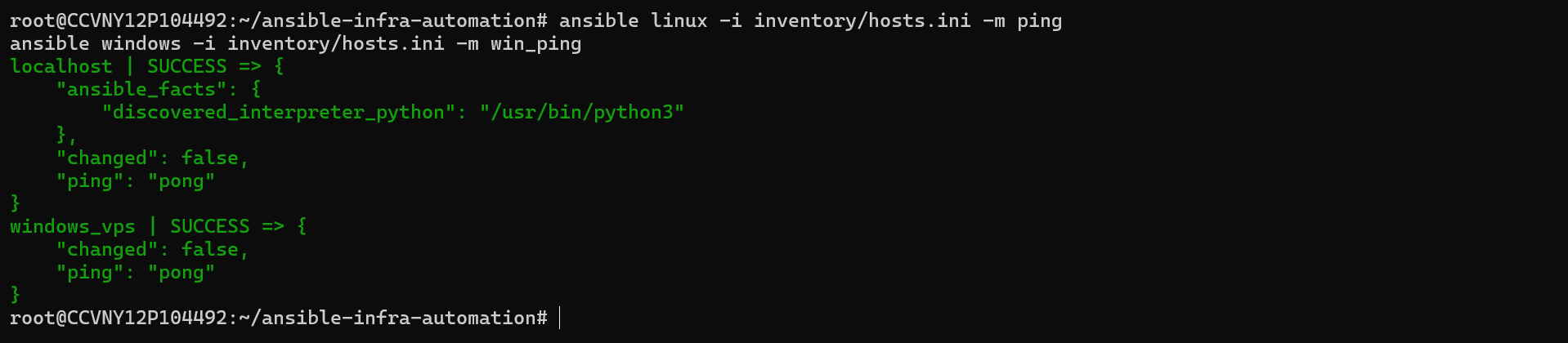
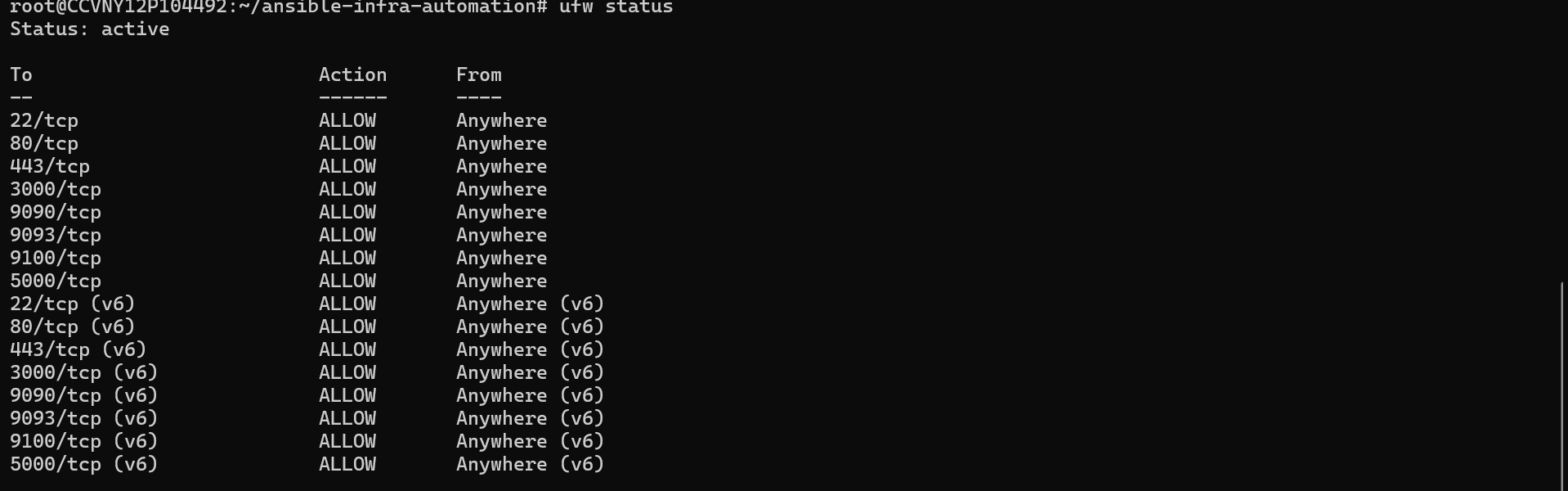
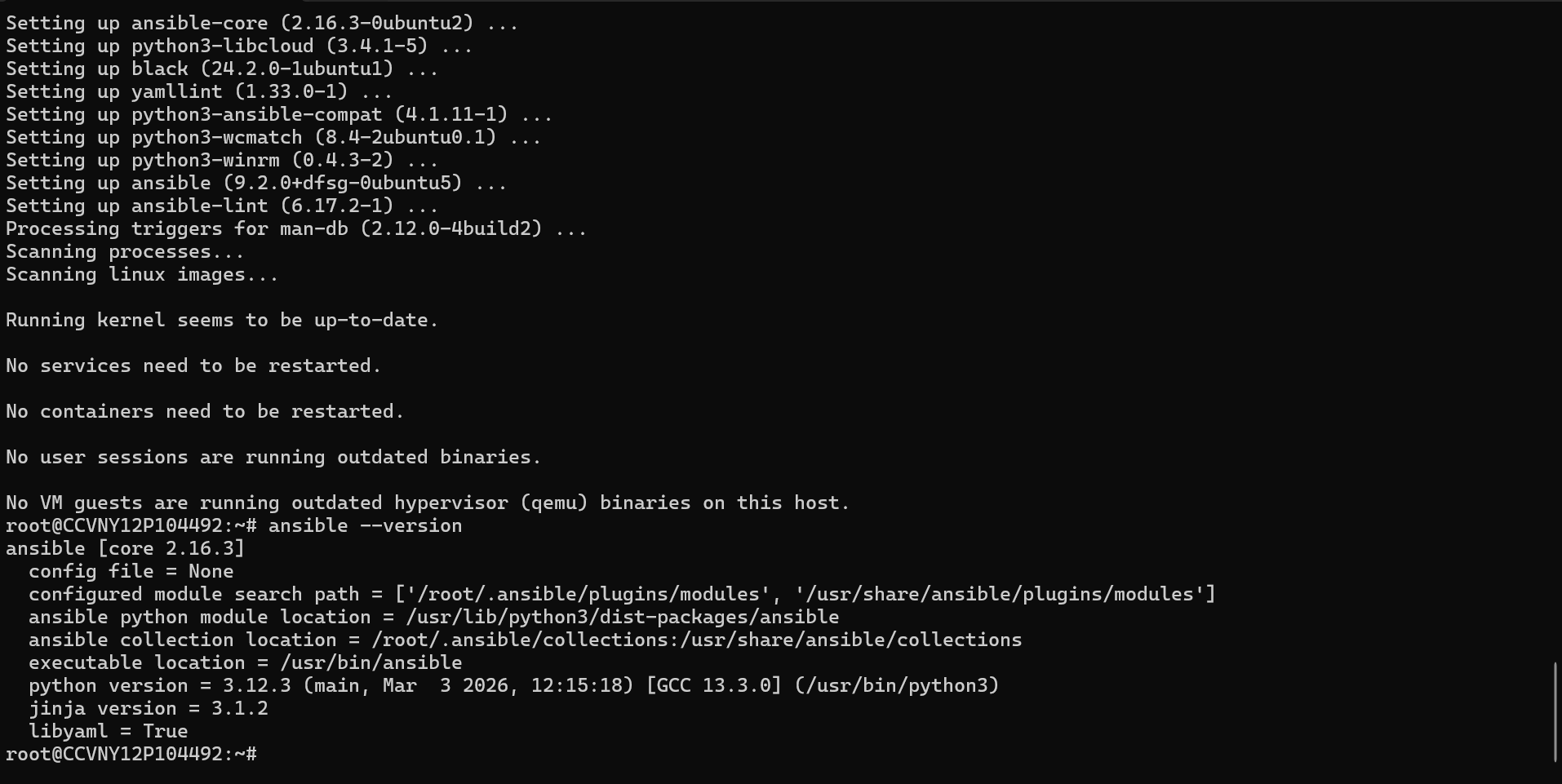
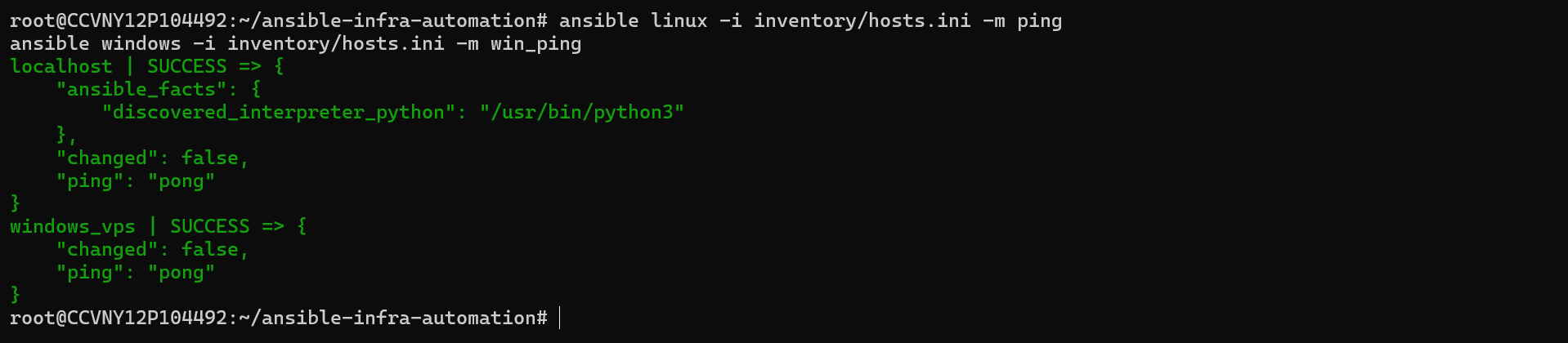
Installed Ansible 2.16 on Linux VPS. Created inventory file targeting both Ubuntu 24.04 (SSH) and Windows Server 2025 (WinRM/NTLM). Verified connectivity with ping and win_ping modules — both returned SUCCESS.
Automated UFW firewall configuration (8 ports), fail2ban setup, SSH password auth disabling, package upgrades, timezone configuration, and common tool installation. All 8 tasks completed with zero failures.
Configured Windows Server 2025 via WinRM — installed IIS and Telnet features, set timezone to UTC, created admin user, configured RDP firewall rule, and installed notepad++, 7zip, and git via Chocolatey.
Encrypted sensitive credentials (Windows user password) using AES-256 Ansible Vault. Vault file committed to git safely — only decrypted at runtime with --ask-vault-pass. Demonstrates security-first infrastructure practices.
Structured project into ansible-galaxy roles (linux_base, windows_base) and a master site.yml that orchestrates all three playbooks in sequence — hardening Linux, configuring Windows, and deploying users — in a single command.
Automated ansible-lint runs on every push via GitHub Actions — enforcing FQCN module naming, YAML truthy value standards, and playbook syntax. CI passes cleanly with Status: Success on every commit.
| Host | OS | IP | Connection | Status |
|---|---|---|---|---|
| linux_vps | Ubuntu 24.04 LTS | 1x1.x4x.1x2.1x | SSH / Port 22 | ping: pong |
| windows_vps | Windows Server 2025 | x7x.2x8.x3x.1x4 | WinRM / NTLM / Port 5985 | win_ping: pong |